Mangan Software Solutions Achieves TÜV Certification for SLM™ Safety Lifecycle Manager
[Houston, October 10, 2023] — Mangan Software Solutions, a leading provider of safety and risk management software solutions, is proud to announce that its Safety Lifecycle Manager (SLM™ v2.5) software has received TÜV re-certification for compliance with the International Electrotechnical Commission (IEC) 61511 standard. This certification represents a significant milestone in Mangan’s commitment to delivering industry-leading solutions that enhance safety and reliability in process industries.
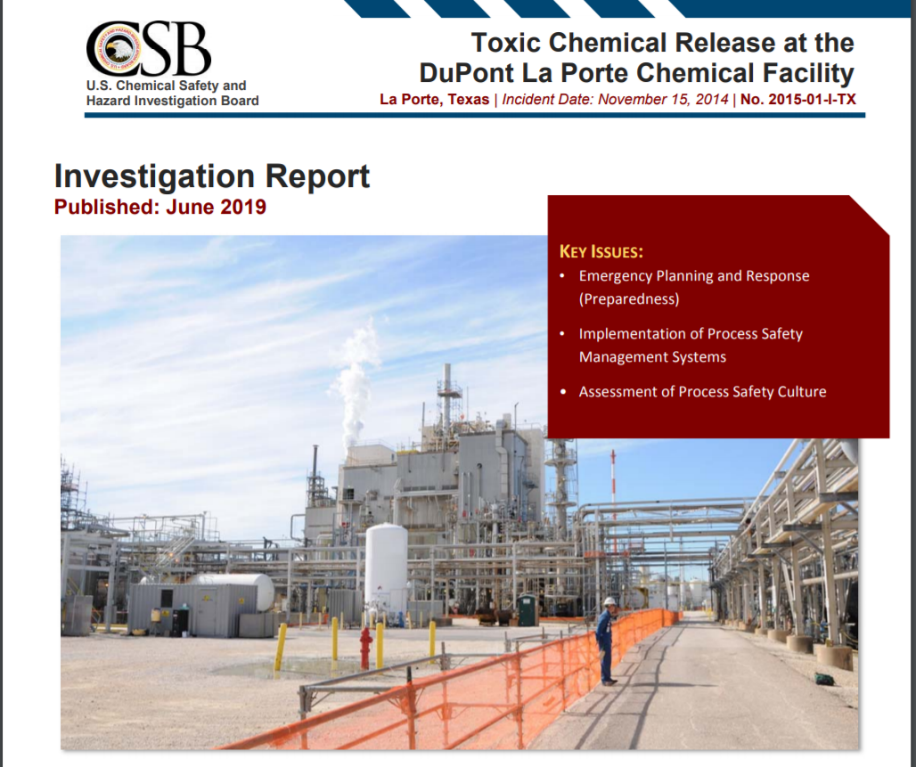
IEC 61511 is a globally recognized standard for the functional safety of safety instrumented systems (SIS) in the process industry. It provides a framework for managing the entire safety lifecycle, from concept to decommissioning, and is crucial for ensuring the safety of critical processes in sectors such as chemical, oil and gas, and manufacturing.
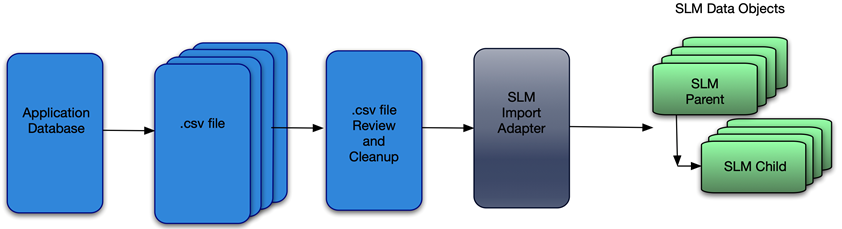
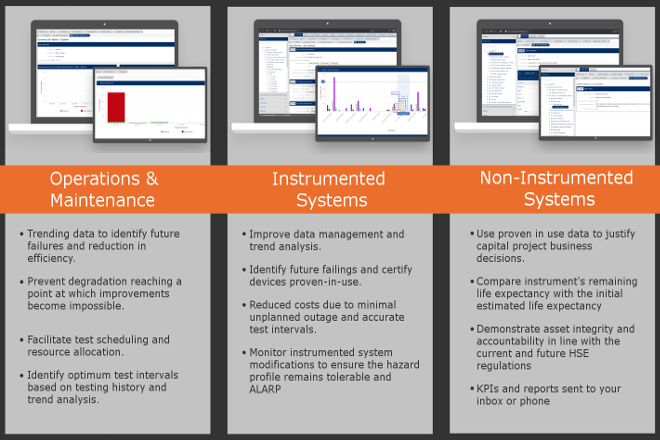
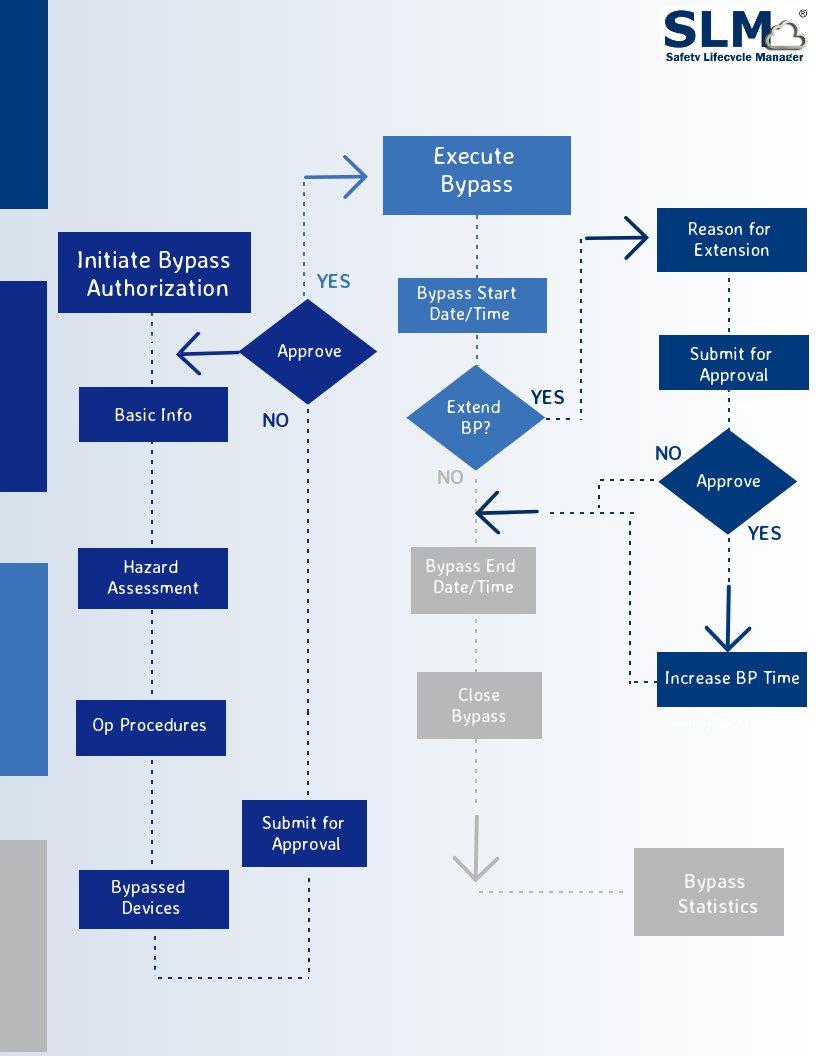
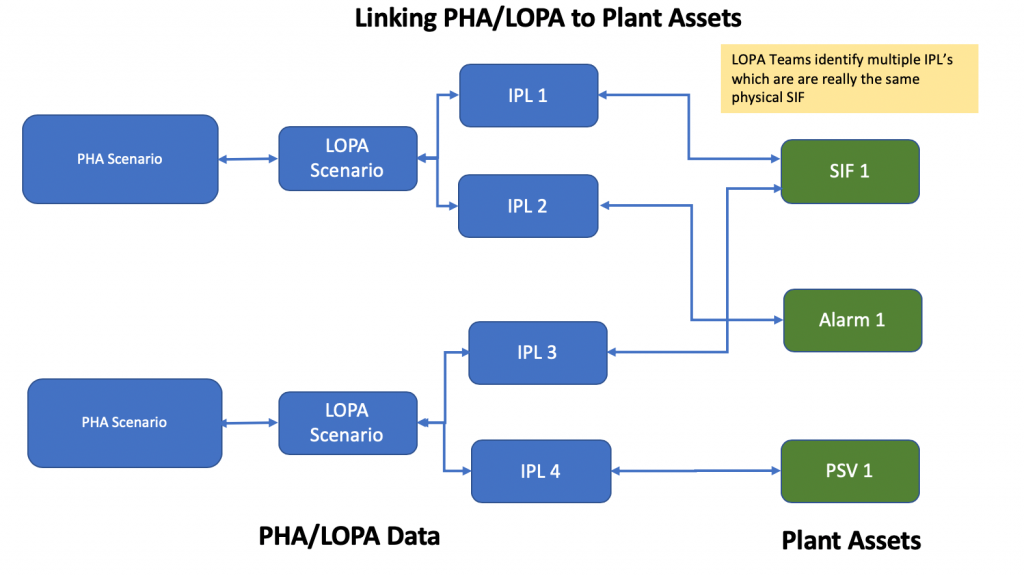
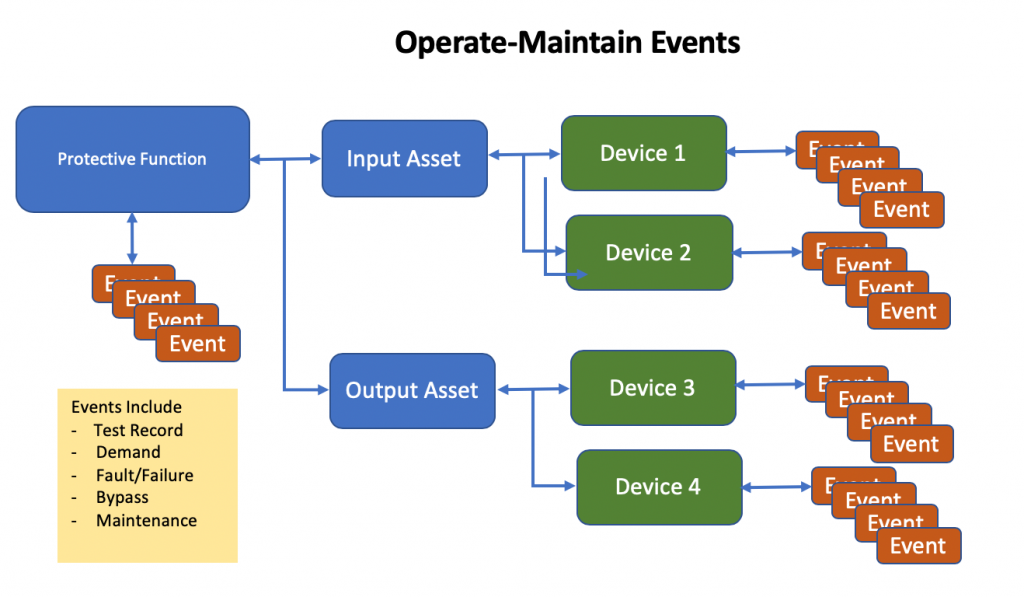
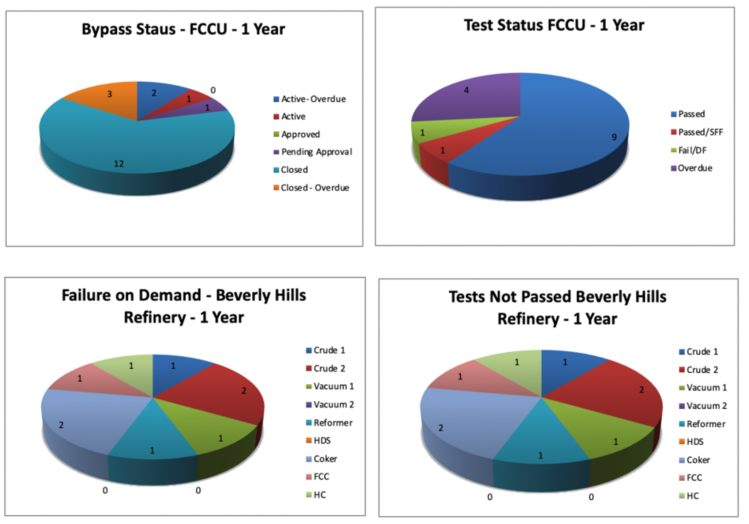
Mangan’s SLM™ software streamlines and automates the complex process of managing safety instrumented systems, enabling organizations to maintain compliance with IEC 61511 efficiently. It provides a comprehensive suite of tools for design, verification, validation, and documentation, helping companies reduce risks, minimize costly errors, and ensure regulatory compliance.
To achieve TÜV re-certification for IEC 61511 compliance, Mangan Software Solutions underwent rigorous testing and evaluation of its SLM™ software by TÜV Rheinland, a globally recognized independent certification body. The successful re-certification underscores the software’s reliability, accuracy, and adherence to international safety standards.
Download TÜV Certificate: https://fs-products.tuvasi.com/certificates?cert_id=10228

“We are thrilled to receive TÜV certification for our Safety Lifecycle Manager software,” said Jeremy Lucas, President & CTO at Mangan Software Solutions. “This achievement reflects our unwavering commitment to providing our customers with best-in-class solutions that enhance safety, reduce operational risks, and streamline compliance processes. With the certification in place, our clients can have even greater confidence in the capabilities of our SLM™ software to meet and exceed industry safety standards.”
Mangan Software Solutions’ SLM™ software offers numerous benefits to organizations, including improved safety, reduced downtime, lower operational costs, and simplified compliance management. Its user-friendly interface and powerful features make it an essential tool for companies seeking to enhance their safety instrumented system performance while ensuring regulatory compliance.
As Mangan Software Solutions continues to innovate and expand its portfolio, the TÜV certification for IEC 61511 compliance further establishes the company as a trusted partner in the safety and risk management space.
For more information about Mangan Software Solutions and its certified Safety Lifecycle Manager software, please visit mangansoftware.com.
About Mangan Software Solutions:
Mangan Software Solutions is a leading provider of safety and risk management software solutions for the process industry. With a commitment to innovation and excellence, the company empowers organizations to enhance safety, reliability, and compliance throughout the entire lifecycle of safety instrumented systems. Mangan Software Solutions’ products and services are trusted by industry leaders worldwide.
Media Contact:
Sean O’Neill
Technical Solutions Engineer
mangansoftware@gmail.com
(281) 402-2647
About TÜV Certification:
TÜV certification is a globally recognized mark of quality and compliance. Organizations that achieve TÜV certification demonstrate their commitment to meeting and exceeding industry standards and regulations, providing assurance to customers and stakeholders that their products or services are of the highest quality and safety. TÜV certification is particularly valuable in industries where safety, reliability, and compliance are paramount, such as the process industry.
| Certificate/Reg.-No. | 968/FSP 1719.01/23 |
Download TUV Certificate: https://fs-products.tuvasi.com/certificates?cert_id=10228